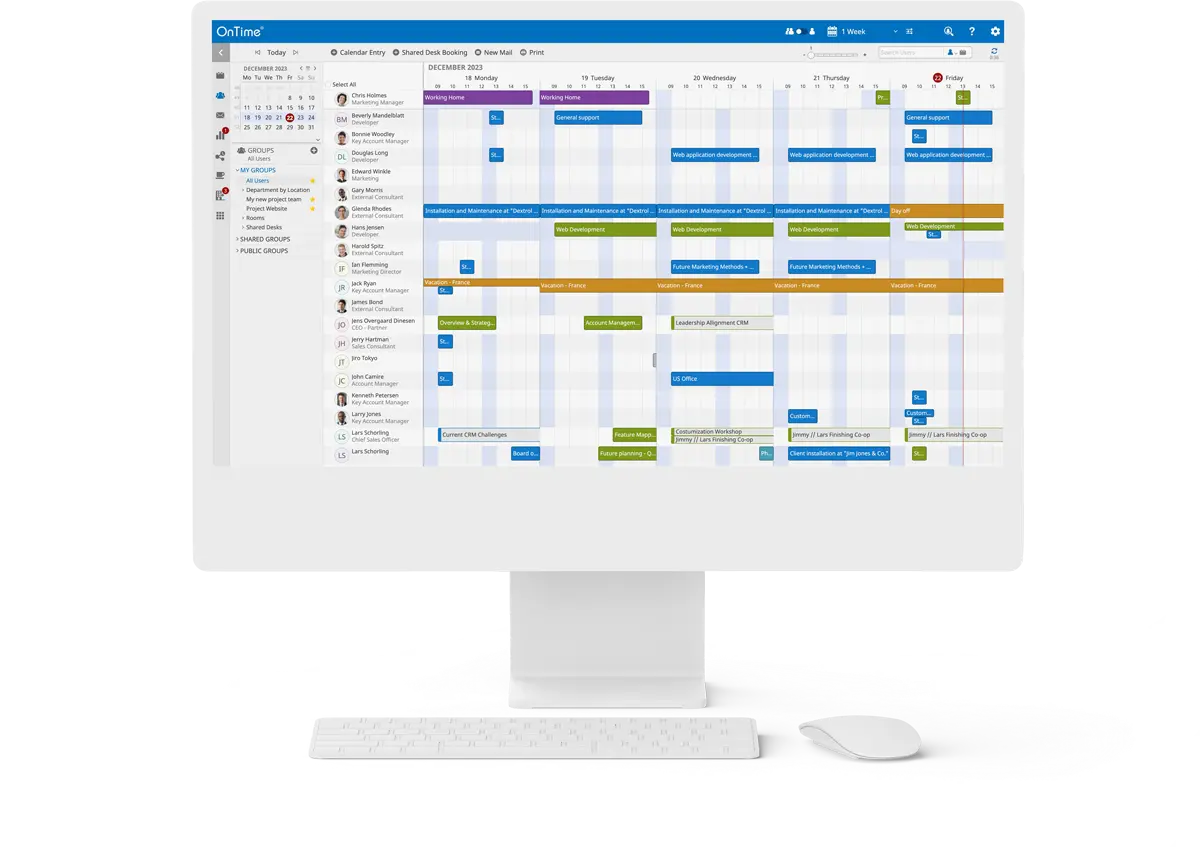

OnTime Group Calendar transforms individual agendas into a synchronised force, aligning thousands of calendars into one harmonious vision.
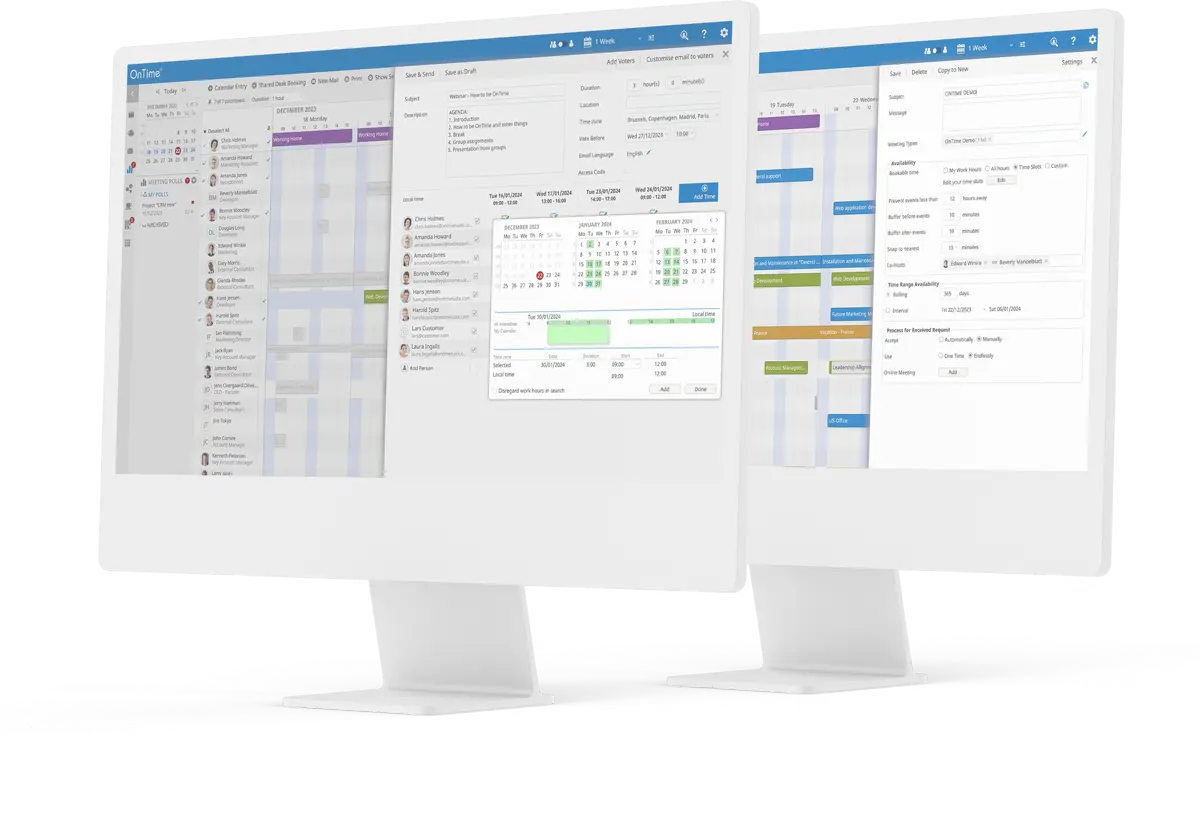
Its multitude of features such as integrated online meetings, legend filters, find time, and vacation planning, make planning both internal and external meetings easier than ever. OnTime Group Calendar is accessible wherever your work takes you, available in your browser and your collaboration platform, or on your smartphone.
Collaboration and diversity are key drivers in achieving successful business outcomes, and that’s precisely what OnTime facilitates.
Access your Group calendar calendar, schedule meetings, and coordinate with your team from any location.
A group calendar make it easy to coordinate meetings, avoid double-booking, and plan group activities.
Provides visibility into everyone’s schedules, promote accountability, and reduce confusion about responsibilities.
Helps to optimise time, offer reminders, and centralise scheduling information, leading to better productivity.
The vacation planning feature offers a time-off view, providing an easy overview of when colleagues are away. together with a simple approval workflow, this assists in optimising resource utilisation and planning on various ooo types of leaves like vacation and maternity leave
This feature integrates the full Group Calendar with Microsoft Teams, facilitating meeting scheduling and finding team members with specific qualifications.
It brings all group calendar features into the MS Teams environment, along with some special MS Teams-specific features, enhancing team collaboration and efficiency
Do you have question? Find the answer here
Microsoft Integration: OnTime integrates with Microsoft’s suite of products, including Office 365 and Exchange on-premises. This integration allows users to view and manage their Microsoft Outlook calendars alongside their colleagues. It also integrates with Microsoft Teams, enabling users to see their team members’ availability and schedule meetings directly within the Teams platform.
HCL (IBM) Integration: For organisations using HCL collaboration tools, OnTime Group Calendar integrates with HCL Notes and Verse mail clients and is from version 14 of the Domino server platform build-in offering a special Freemium edition. This integration ensures that users can seamlessly manage their schedules and coordinate with colleagues who are using the HCL platform.
Cross-Platform Support: For organisations that use a combination of Microsoft and HCL products, OnTime supports a hybrid environment, allowing seamless integration across different platforms.
OnTime offers a range of support and training resources to assist users in effectively utilising their group calendar system. These resources are designed to provide both technical support and user education, ensuring that organisations can maximise the benefits of the OnTime Group Calendar. Here’s an overview of the support and training resources available:
Tutorial Videos: OnTime offers concise, step-by-step tutorial videos, simplifying learning for users by visually demonstrating the system’s features and functionalities.
Documentation: Comprehensive user manuals, installation guides, and best practices are available, catering to both end-users and IT professionals for effective system management.
Technical FAQs: A dedicated FAQ section provides quick answers to common questions, aiding in immediate problem-solving and user support.
Release Notes: Release notes detail new features, enhancements, and bug fixes in each software update, keeping users informed about the latest changes.
Support Tickets: Users can submit support tickets for personalized assistance with specific issues or challenges encountered while using OnTime.
Downloads: Access to the latest software versions, updates, and patches ensures users have the most current and secure OnTime experience.
User Interface Customization: Adjust the calendar’s appearance to align with your company’s branding and user preferences.
Feature Selection: Enable or disable specific features like room booking or shared desks to suit organizational needs.
Integration Capabilities: Seamlessly integrate with Microsoft Office 365, Exchange, and HCL Domino for streamlined workflows.
Access Control and Permissions: Set user access levels and permissions in line with company hierarchy and privacy policies.
Add-Ons and Extensions: Enhance functionality with add-ons like voting, catering management, and visitor tracking.
Scalability: Scale the system to fit the size of your organization, from small businesses to large enterprises.
Localization: Supports multiple languages, catering to international companies or diverse workforces.
OnTime Suite’s pricing is scalable, depending on organisation size and chosen calendar features, with specific tiers for small, mid-size, and large businesses.
We offer OnTime both on a perpetual and subscription basis. Calculate your own price on our Pricing page.



Here are some price examples on how much it costs using OnTime. Click on the “Find My Price” below to see what your price is.
Both subscription and perpetual options are available.

OnTime Group Calendar ApS
Venlighedsvej 6 | 2970 Hørsholm, Denmark
CVR: DK 1935 2838 | Phone: +45 70 23 23 40
By signing up for this event, you agree to be added to our newsletter mailing list. We will use your email address to send you updates, news, and offers. You can unsubscribe anytime via the link in any email.
For more information on how we process and safeguard your data, please read our Privacy Policy.
By signing up for this event, you agree to be added to our newsletter mailing list. We will use your email address to send you updates, news, and offers. You can unsubscribe anytime via the link in any email.
For more information on how we process and safeguard your data, please read our Privacy Policy.